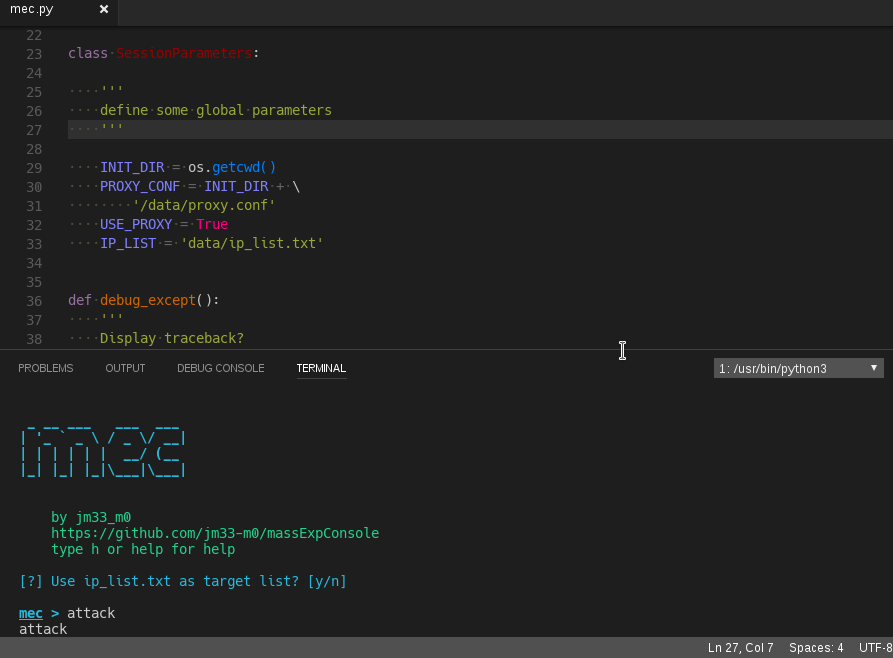
MassExpConsle - User Guide
https://github.com/jm33-m0/massExpConsole
thank you all for your support
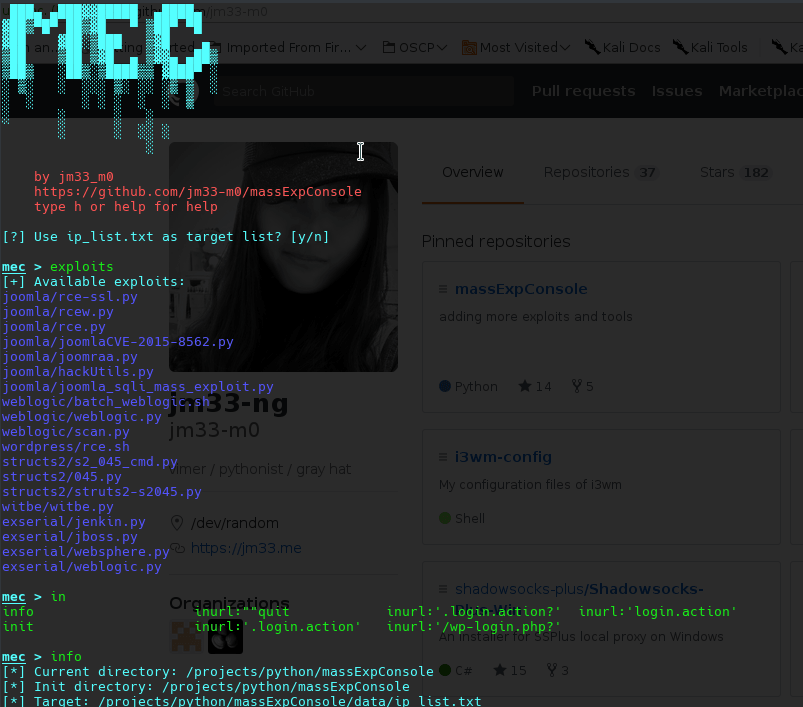
what it does
- an easy-to-use cli ui
- execute any adpated exploits with process-level concurrency
- some built-in exploits (automated)
- zoomeye host scan (10 threads)
- google page crawler with gecko and firefox (not fully working)
- a simple baidu crawler (multi-threaded)
- webshell …