Fully Interactive Remote Shell for Windows
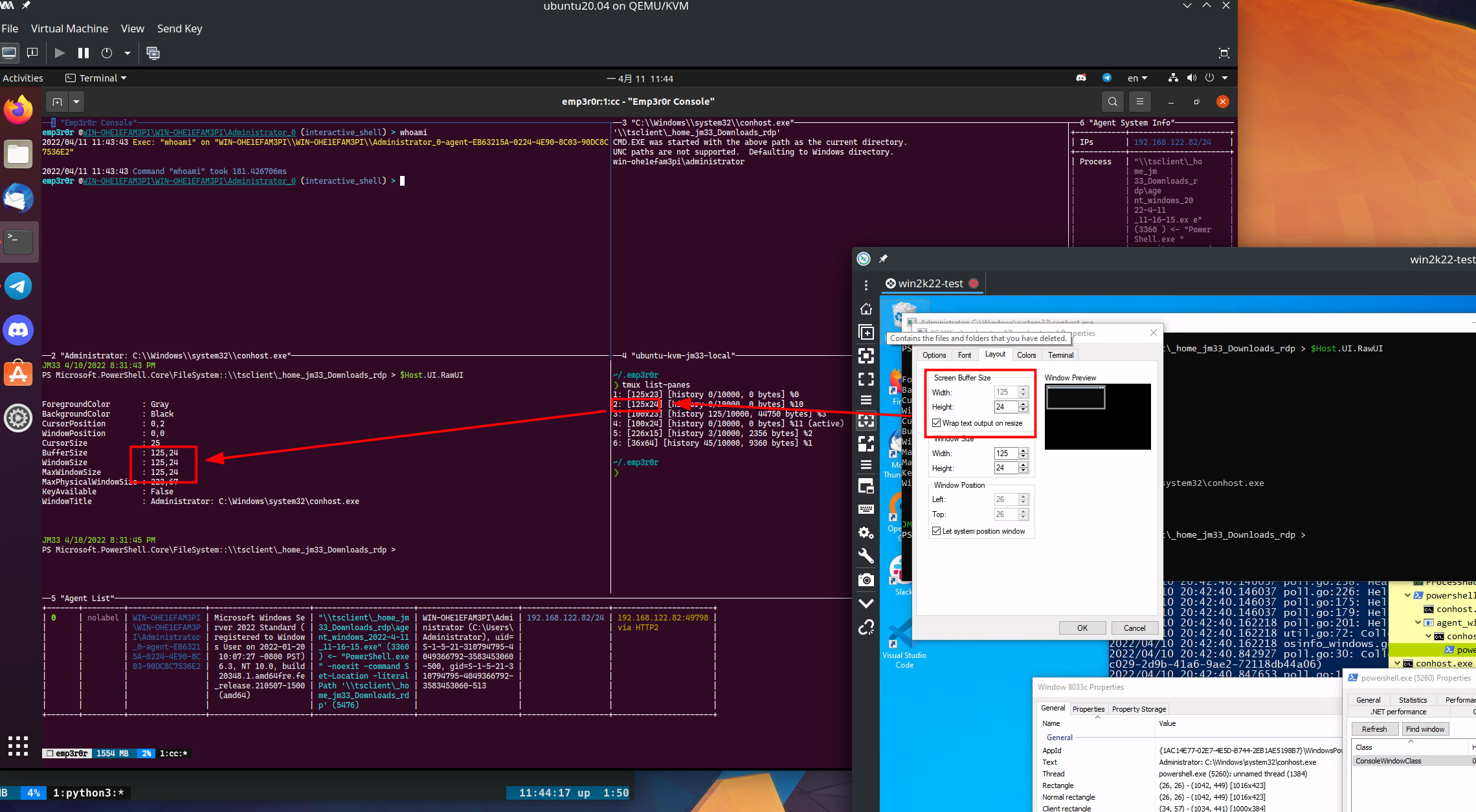
Understanding Windows Console Host
If you open cmd.exe or powershell.exe in Windows, you will always find conhost.exe alongside them. As a matter of fact, conhost.exe has been around for more than a decade. Every (console based) Windows program has a "console" with them, for example when …